Static Agent for Docker
Agent Deployment
Static Agent for Docker
Product Documentation
Product Improvements
Static Agent for Docker
Agent Deployment
Static Agent for Docker
| Admin | Co-admin | Asset Manager | Viewer | ||
|---|---|---|---|---|---|
| Agents | Add | ||||
| Edit | (Agent Name Blocked) | ||||
| Delete | |||||
| Probing Distributions | Add | ||||
| Edit | |||||
| Delete | |||||
A variety of agent software is provided that supports deployment in heterogeneous network environments. Dockerized static agents enable deployments to the existing infrastructure without purchasing additional host device hardware.
Cisco Catalyst 9300, 9500 with the following available system resources are thoroughly tested and verified.
Create an agent for each host device
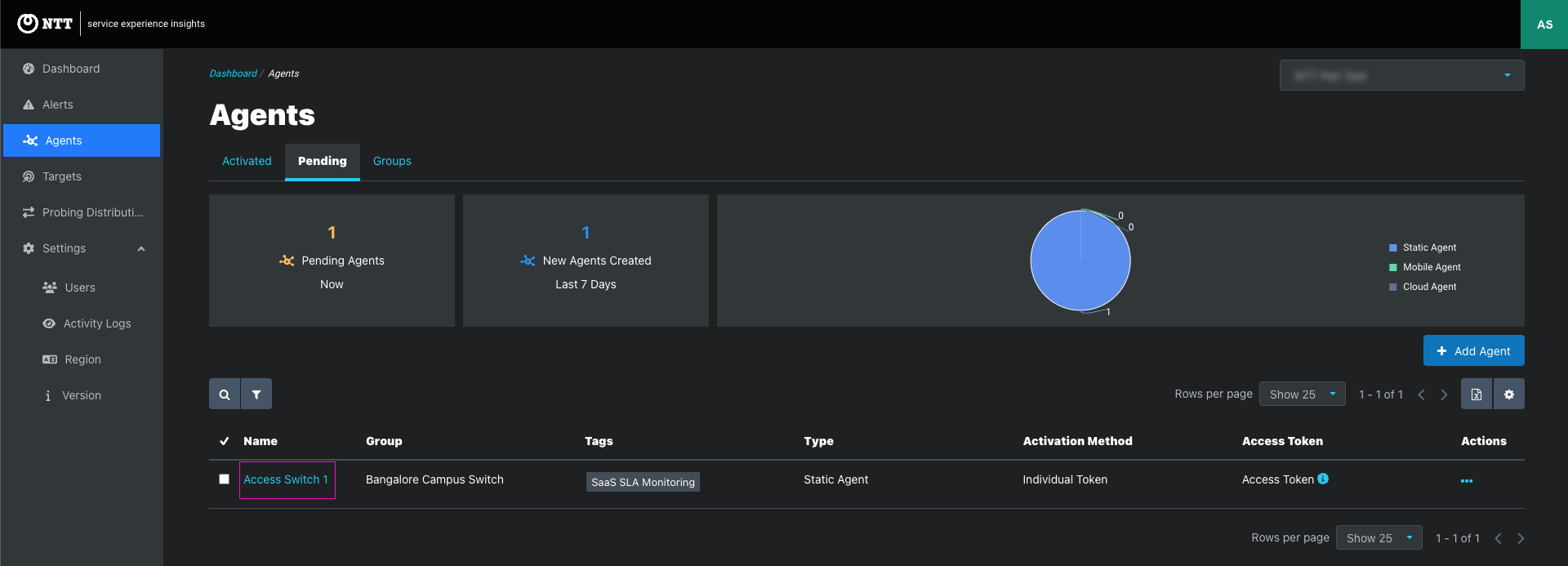
Click the Add Agents button on the Agents page
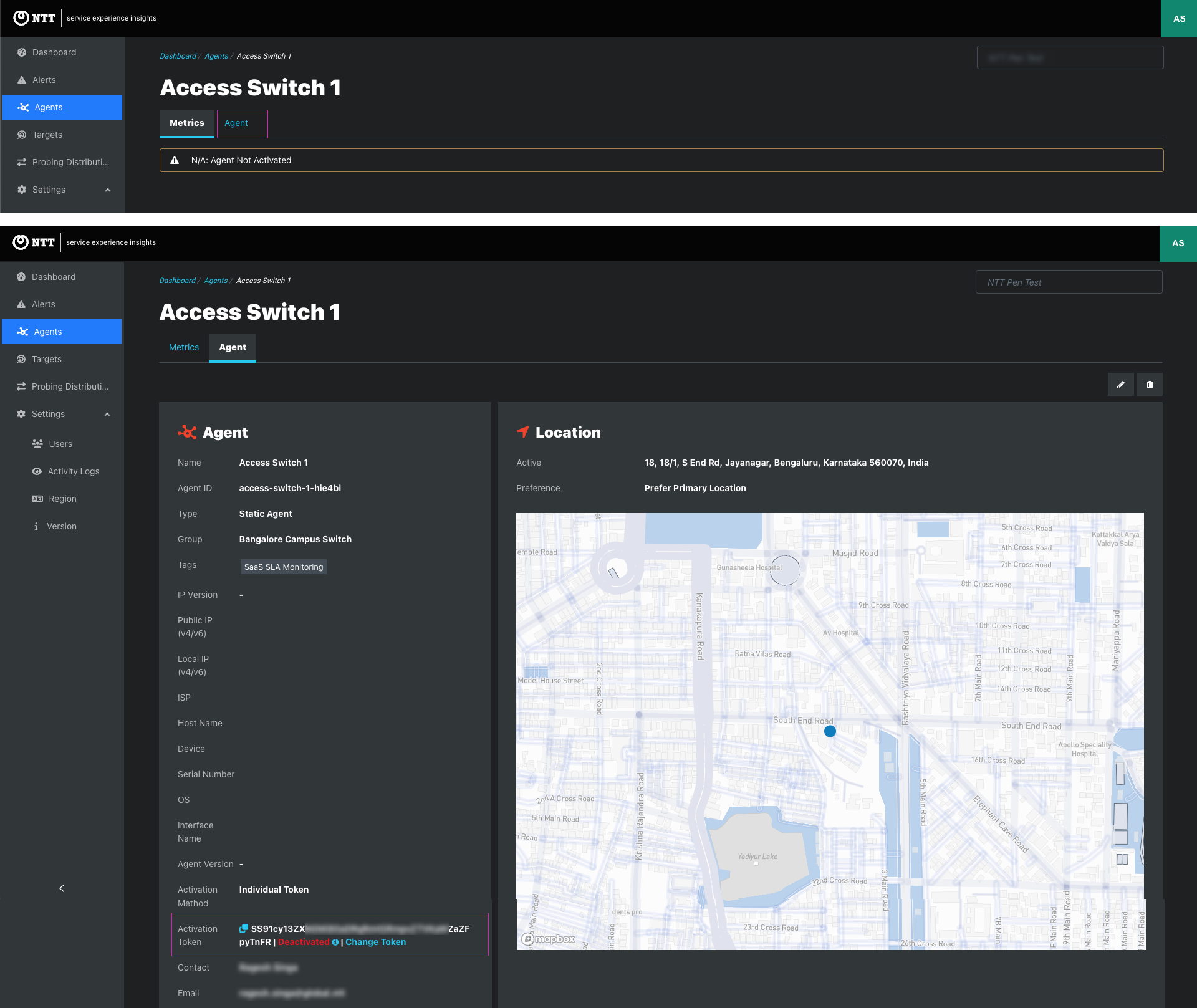
Following are agent configurations for this deployment. See the Agents article for more information about agent configuration
| Input | Input Type | Options | Instructions | Required |
|---|---|---|---|---|
| Name | Text | -- | Enter a display name for the agent.
| Required |
| Group | Single select dropdown | Select an existing group |
| |
| Tags | Multiselect dropdown | Select an existing tag or add a new tag |
| |
| Type | Single select dropdown |
|
| Required |
| Enable As Target | Checkbox | Unchecked (default) |
| |
| IP Type | Single select dropdown |
|
| Required for target-enabled agents only |
| IP Version | Single select dropdown |
|
| Required for target-enabled agents only |
| Target Protocol | Multiselect dropdown |
| Select one or more target protocols for this managed target agent. | Required for target-enabled agents only |
| UDP Port | Text | 5001 (default) | Enter UDP Port | Required for target-enabled agents only |
| Speed Test port | Text | 8080 (default) | Enter Speed Test port | Required for target-enabled agents only |
| Activation Method | Single select dropdown |
|
| Required |
| Location Preference | Single select dropdown |
|
| Required |
| Location | Text | -- |
| Required for:
|
| Contact Name | Text | -- | Enter the contact name of the person responsible for activating agent software. | |
| Text | -- | Enter the email address of the person responsible for installing and maintaining the agent software. | Required | |
| Email Language | Single select dropdown |
| Choose the language for the agent activation email | Required when Individual Token selected |
| Skip Activation Email | Checkbox | Unchecked (default) | Unless checked, Individual Tokens are automatically emailed to the email address in the client record. |
Fetch Activation Token
Deploy Agent Image for IoS XE
docker pull cloudwan/watchdogagent:latest
docker save cloudwan/watchdogagent -o watchdogagent.tar
run-opts 1 "-e ACTIVATION_TOKEN=<activation token value>”
Local Dashboard: Advance Settings->Docker Options ->Input
--rm -e ACTIVATION_TOKEN=<activation token value>
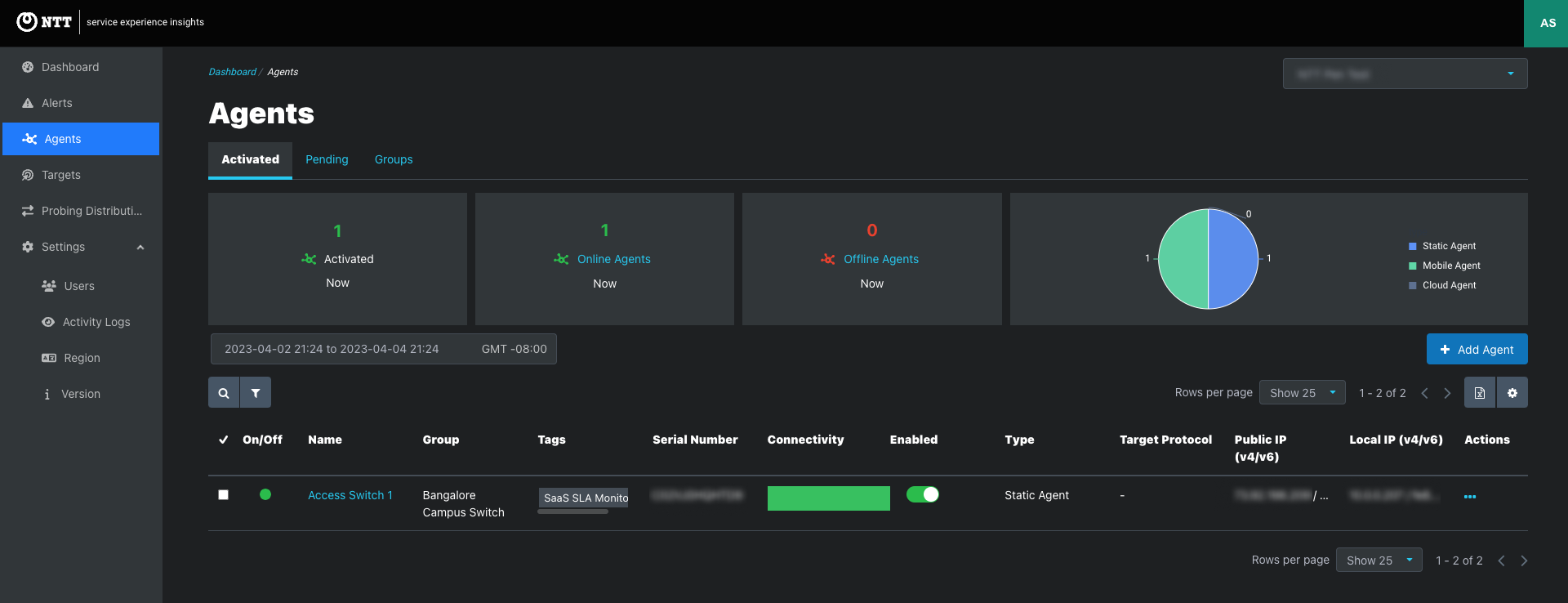
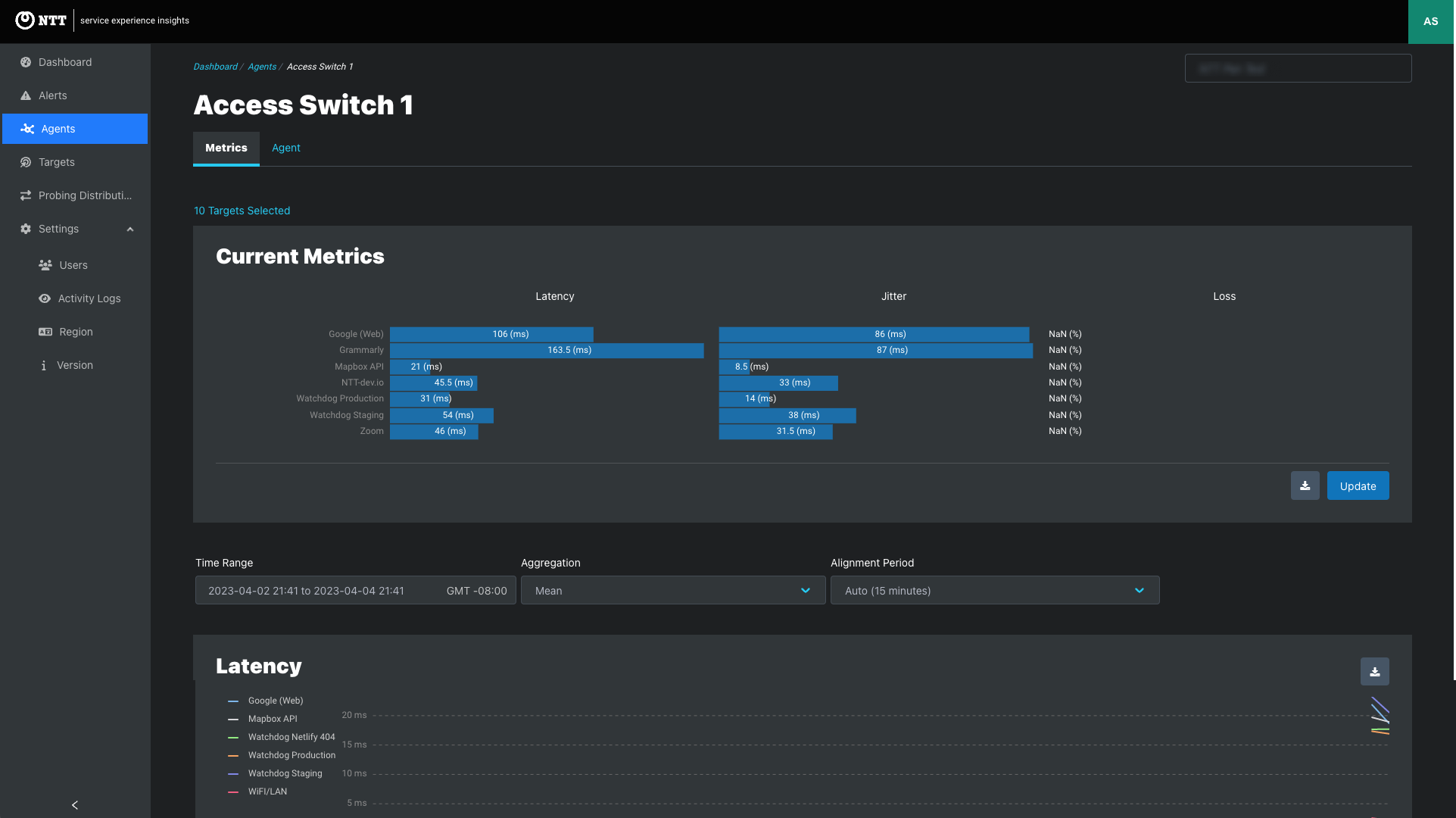
Wait five minutes and check the SEI dashboard to confirm successful activation.
In This Article
